Backup Service
NetApp Products and Solution
Backup Service
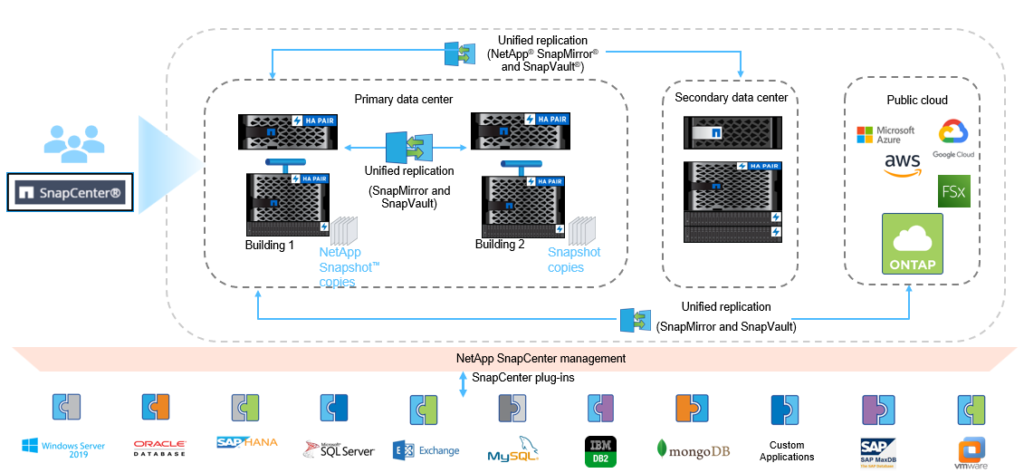
SnapCenter®
SnapCenter provides host-based data management of NetApp storage for all SAP supported databases . It offers application-aware backup and clone management, and it automates fast error-free data restores.
What if you could…?
- Easily manage data protection and clone lifecycles across the hybrid cloud
- Protect your applications with improved RPO/RTO
- Accelerate application development and speed products to market
- Increase IT efficiency by delegating common storage tasks

SnapCenter Software is:
End-to-end protection and copy management for data anywhere in the Data Fabric
Cloud Backup
Backup Business Challenges
The traditional ones
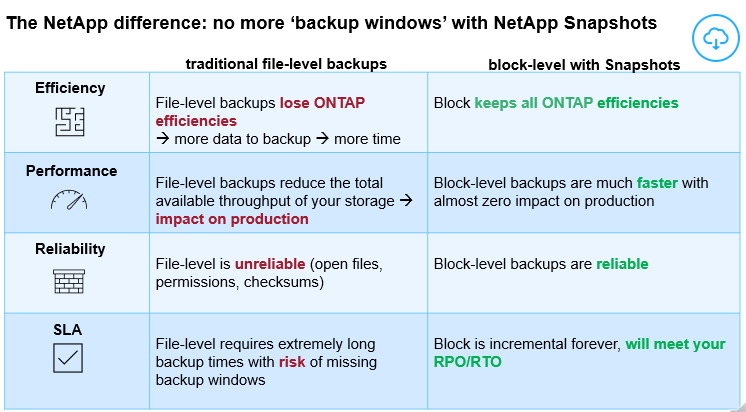
Eliminate
‘backup windows’ forever
The NetApp difference: no more ‘backup windows’ with NetApp Snapshots
NetApp Cloud Backup
Cloud Backup delivers seamless and cost-effective backup and restores capabilities for protecting and archiving both Cloud and On-Premises ONTAP data.
Automated, set-and-forget, backups
Drastically reduced backup times
Reliable, block-level protection
Reduced costs with object and cloud archive storage options
Instant restores with searchable indexed catalog
Limitless scalability
ONTAP storage efficiencies
Kubernetes protection
Dark sites support
Unmatched efficiency
Average
90%
less network traffic
Less overhead
At least
10x
Faster backups
Easy to operate
less than
2 min
Setup time
Simple to activate
only
1 click
Activation
Data Migration / Replication
SnapMirror
SnapMirror Data Replication
SnapMirror is a feature of ONTAP that delivers high-speed, efficient, and secure data transport for enhanced site-to-site failover and disaster recovery. You get efficient, array-based replication for backup and disaster recovery across the data fabric.
An effective disaster recovery (DR) solution protects data against system failures, power failures, and site failures. You can boost cost efficiency and get maximum return on your investment if that solution can also reduce costs and let you use your DR facility for business intelligence. Such cost efficiency makes it easier to provide DR for more of your data. Although backups can help you recover lost data from an archival medium such as tape, disk, or the cloud, mirroring is the most popular data availability mechanism for business continuity and disaster recovery, especially if you would like to minimize downtime.
NetApp® SnapMirror® is disaster recovery technology, designed for failover from primary storage to secondary storage at a geographically remote site. SnapMirror replicates data at high speeds over LAN or WAN, so you get high data availability and fast data replication for your business-critical applications, including Microsoft Exchange, Microsoft SQL Server, and Oracle, in both virtual and traditional environments. And when you replicate data to one or more NetApp storage systems and continually update the secondary data, your data is kept current and remains available whenever you need it. No external replication servers are required.
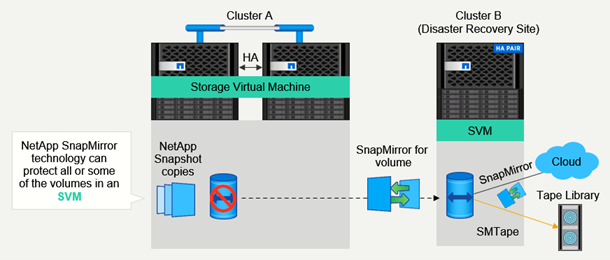
Figure 1: NetApp SnapMirror replication overview.
Maximize Uptime and Accelerate Your Business with NetApp SnapMirror
You can increase availability and speed disaster recovery with NetApp SnapMirror software. SnapMirror is a cost-effective, multipurpose solution that replicates data at high speeds over LAN or WAN. It provides you with rapid recovery for your business-critical applications and data migration, in both virtual and traditional environments. SnapMirror is used by more than 13,000 businesses around the globe, protecting more than 669 petabytes of used data using asynchronous replication.
With SnapMirror, you can:
- Keep your business running
- Lower your TCO
- Increase efficiency
Keep Your Business Running in the Event of a Disaster
SnapMirror speeds data replication, enabling you to complete transfers more frequently and lower recovery point objectives. SnapMirror also speeds recovery, so users can be reconnected to the most current data and get back to business more quickly after a catastrophic failure or disaster. You can:
- Easily manage replication between storage endpoints, from flash to disk to cloud
- Transport data seamlessly and efficiently between NetApp storage systems to support both backup and disaster recovery with the same target volume and I/O stream
- Failover to any secondary volume
- Recover from any point-in-time NetApp Snapshot™ copy on the secondary storage
- Safeguard your most critical workloads with available zero-data–loss synchronous replication (RPO=0)
“NetApp [SnapMirror] takes care of automating replication and recovery processes…Should we ever experience a site disaster, in a matter of minutes we can be up and running at the DR facility. And it costs us about 50% less than before.”
-Dale Martinson, Manager of Systems and Security, DCI
Lower TCO and Boost ROI
SnapMirror can help reduce total cost of ownership (TCO) by up to 60%. Since data is stored natively, with features such as NetApp FlexClone® technology, you can create near-instantaneous, space-efficient copies of data on your secondary or tertiary storage. You can use these copies for multiple business functions without any negative effect on your production system.
You can use SnapMirror as a single replication tool across your entire NetApp ONTAP® clusters. Deploy SnapMirror in minutes and integrate it with Active IQ Unified Manager to automate ongoing replication and management tasks, further simplifying and reducing administrative workloads.
“With the common operating system across all controller heads, our storage system is easier to manage than other systems of the same size. With NetApp®, we deliver 100% uptime.”
-Mark Tuttle, Senior Manager of Engineering, AutoTrader.com
Increase Efficiency
Thin replication and native network compression reduce bandwidth utilization and reduce secondary storage requirements for backup and disaster recovery. With SnapMirror software, you can leverage one thin replication data stream to create a single repository that maintains both the active mirror and prior point-in-time copies, reducing network traffic by up to 50%.
“With NetApp, we were able to avoid $150,000 to $200,000 in infrastructure costs because we didn’t have to install a Fibre Channel storage network at our secondary site.”
-Whitney Kuszmaul, Network Manager, Cleveland Indians
Cloud Sync
Cloud Sync Service: Smooth and Secure Data Synchronization
Cloud Sync service is an easy-to-use cloud replication and synchronization service for transferring files between on-premises NFS or CIFS file shares, Amazon S3 object format, Azure Blob, Google Cloud Storage, IBM Cloud Object Storage, Cloud Volumes Service, Azure NetApp Files, or NetApp StorageGRID®. Cloud Sync quickly and securely moves the files to where you need them.
Transferring data between disparate platforms and maintaining synchronization can be challenging for IT. Moving from legacy systems to new technology, server consolidation, and cloud migration, require large amounts of data to be moved between different domains, technologies, and data formats. Existing methods such as relying on simplistic copy tools or homegrown scripts—that must be created, managed, and maintained—may be unreliable or not robust enough, and can fail to address challenges such as:
- Getting a dataset to the new target effectively and securely
- Transforming data to the new format and structure
- Having a timeframe and keeping data up to date
- Managing the cost of the process
- Validating migrated data consistently and completely
Cloud Sync gives you the ability to:
- Migrate data incrementally to and from NFS, CIFS, Amazon S3, Amazon EFS, Azure Blob storage, Google Cloud Storage, Cloud Volumes Service, Azure NetApp Files, NetApp StorageGRID Webscale appliance, or any other cloud provider object store
- Consolidate data from multiple systems into a single repository
- Facilitate greater collaboration between data personnel
- Move workloads to the cloud strategically
- Tier data to capacity storage to free up space in performance tier systems
- Archive data for compliance or regulatory purposes
- Use AWS Azure or Google Cloud for long-term data management or access by other cloud services, such as data analytics
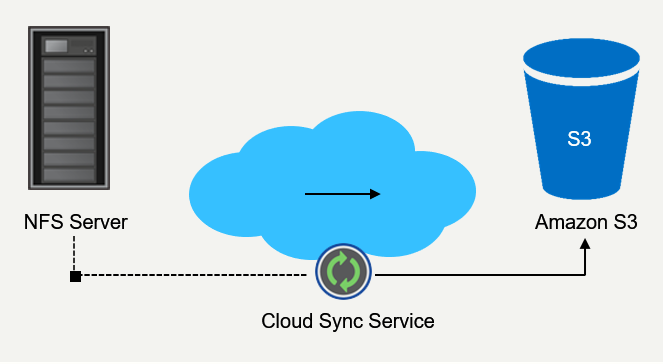
Cloud Sync provides multiple advantages for your business:
- Quick, simple, and easy to operate
- Safe and secure
- Smooth integration
- Cost effective
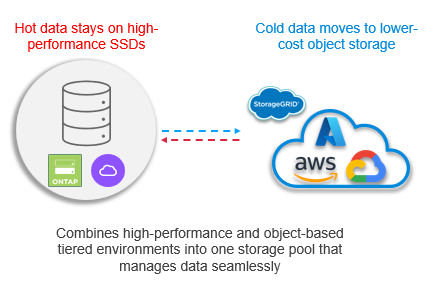
Cloud Tiering
NetApp Cloud Tiering
Intelligent Data Growth Management
NetApp solves the most pressing data management challenges
Mange your entire hybrid/multicloud data storage infrastructure efficiently
Cloud Tiering = Intelligent Data Growth Management
- Discover
- Identify your ONTAP-based clusters/volumes
- Tier
- Set target ONTAP object-based storage
- Define data tiering policies
- Manage
- Adjust policies as necessary
- We’ll take it from here
- Sit back and relax
- You get more storage for less cost
Compliance & Security
ONTAP Ransomware detection
→ blog
SnapLock
NetApp compliance solution
Write-once, read-many (WORM) offering fully integrated into NetApp® ONTAP® 9

NetApp® SnapLock® volumes
Compliance volumes
(disk level protection)
and
Enterprise volumes
(file level protection)
Supported administration models
NetApp SnapLock
Compliance
and
SnapLock Enterprise
Certified data compliance
NetApp SnapLock is certified to meet stringent industry requirements, such as the SEC 17a-4(f) rule, FINRA, and CFTC.
NetApp ONTAP 9 SnapLock
Two retention models, one software license*
NetApp® SnapLock® Compliance
NetApp All Flash FAS, FAS
- Deployed for strict regulatory requirements such as SEC17a-4 and CFTC rule 1.31(b)
- Administrator is not trusted to perform delete operations
- All user and administrative operations are protected
- Aggregate rename now allowed (ONTAP 9.8 and later)
- Volume and aggregate deletion not allowed before expiration
- Zeroing disks and sanitizing not allowed
SnapLock Enterprise
All Flash FAS, FAS, NetApp ONTAP® Select
- Deployed for flexible regulatory requirements and organization-defined policies
- Administrator is trusted to perform delete operations (privileged delete)
- Administrative operations are
allowed (but securely recorded) - Volume and aggregate rename allowed
- Volume and aggregate deletion allowed before expiration
- Zeroing disks and sanitizing allowed
Cloud Secure
Why Cloud Secure?
- Detect ransomware attacks before it’s too late
- Minimize the impact of an attack with automatic data backup
- Gain visibility into malicious user activity and identify potential policy risks
- Easily satisfy audit reporting requirements saving time & money
- Simple SaaS solution, quick time to value, no upgrades, scalable from single departments to global enterprises
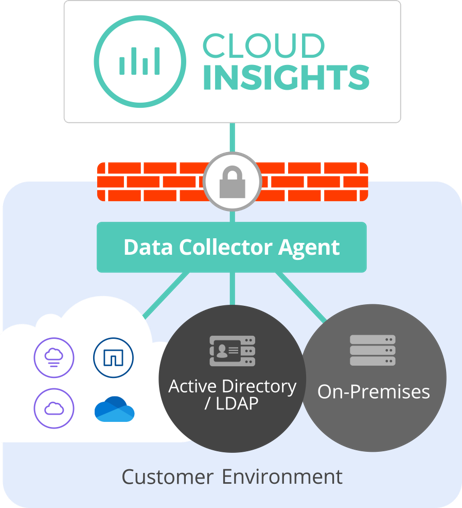
How Cloud Secure Works
Cloud Secure does not assume a trusted internal network, it takes a trust no one approach. It inspects and analyzes all data access activity in real time to detect malicious behaviors.
Monitor User Activity
To accurately identify breaches, every user activity across on-premises and hybrid cloud environments, is captured and analyzed.
Detect Anomalies & Identify Potential Attacks
Cloud Secure uses advanced machine learning algorithms to uncover unusual data activity and detect a potential attack.
Automated Response Policies
Cloud Secure alerts you and automatically takes a data snapshot when detecting a risky behavior, making sure your data is backed-up and you can recover quickly.
Forensics and User Audit Reporting
Provides a graphical interface to cut and slice activity data to perform data breach investigations and generate User Data Access Audit reporting.
Cloud Data Sense
Let us do the hard work
Empower Data Governance and Compliance Teams
Automate the inefficient processes that take weeks down to minutes
Ensure Sensitive Data Is Stored Where You Want It
Protect your IP and enforce restrictions on sensitive data
Stay Optimized, Save Money
Get an up-to-date view of what kind of data makes up the storage footprint
Maintain Constant Control
Maintain visibility of all sensitive data on systems to reduce risk of privacy breaches.
Maintain Compliance
Get reports that prove your organization is compliant in seconds not weeks
Maintain
Governance
- View insights on redundant and stale data to optimize storage costs
- Understand what sensitive data is not secured
- Receive alerts if sensitive data needs attention
Demonstrate
Compliance
- Empowers enterprise storage and IT management teams to take control of data and deliver direct value in supporting data Compliance and Governance efforts in real-time and with no extra effort.
Automate Repetitive
Daily Tasks
- Run compliance reports instantly
- Share insights and information seamlessly.
- View up to date information on your storage footprint and what needs attention
- Turnaround ad-hoc requests for information in minutes not weeks
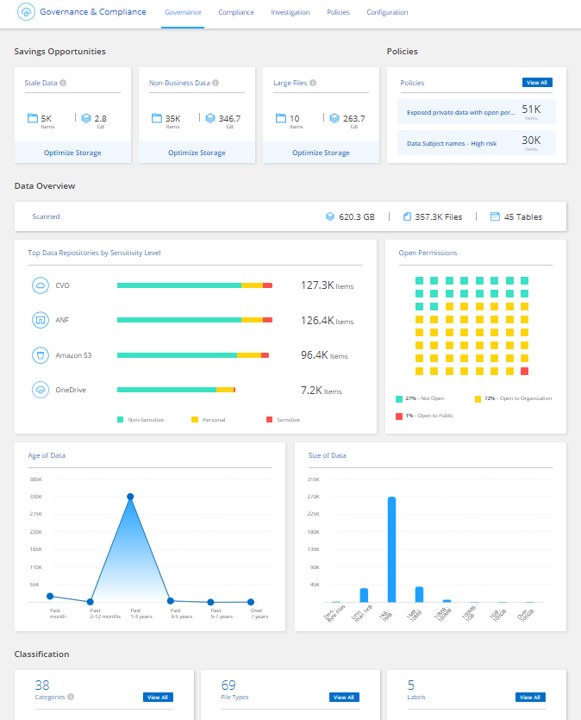
Cloud Data Sense Key Use Cases
Customer Benefits
- Efficiency
- Eliminates manual and repetitive governance and compliance tasks
- Generate compliance reports in minutes not weeks
- Immediately identifies security risks and alerts you when potential risks need attention
- Locates all data on a certain subject with a click of a button
- Governance
- Maps all data
- See stats on sensitive and non-sensitive data
- Highlights redundancies for optimization opportunities
- Drilldowns for detailed insights
- Visibility
- See what sensitive data is not secured correctly for risk prevention
- Data is automatically classified and categorized based on its contents to easily identify what makes up the storage footprint
- Seamlessness
- Simply turn it on to get started and view dashboards instantly